Identify exposed assets within your environment using Picus Attack Surface Validation (ASV). This visibility feeds into Picus Exposure Validation, uncovering potential entry points and offering critical business context to calculate the Picus Exposure Score.
Automated Security Validation for Measurable Risk Reduction
Your Tools Are Only as Strong as Their Last Test
You’ve invested in NGFW, EDR, SIEM, email security, and maybe more.
But when did you last validate they actually work as intended?
With Automated Security Validation (ASV), you’ll know:
- which controls fails and why
- when not to spend extra time
- which fixes reduce most risk

How Does Automated Security Validation Work?
ASV safely executes real-world attack techniques in your environment and measures how your security controls respond to them. It’s continuous evidence of your control effectiveness.
Disclosed
Scoring
High Priority
the Attack
Detection Results
Verify
Applied
Remediation
Priorities
Key Features of ASV Platform
Whether you’re a team of 3 or 30, we help you validate continuously without increasing your workload.
Continuous & Automated
Production-Safe Execution
Vendor-Specific Remediation
Emerging Threat Coverage
Reduced Manual Effort
Executive-Ready Reporting
AI-Driven Security Validation
.png?width=2162&height=1500&name=Copy%20of%20platform-page-banner-video%20(5).png)
Leverage AI to transform how you detect, validate, and prioritize threats.
-
Generate attack scenarios from any threat intelligence report using AI-driven automation.
- Continuously learn from validation data to refine detection logic and improve defense performance.
- Focus analyst effort where AI-powered analysis proves the greatest impact.
Unified Platform for All Validation Needs
All integrated. One data fabric. One workflow.
Because if security validation stops at a single layer, you will outgrow it.
-1.webp?width=1400&height=900&name=Visuals02%20(1)-1.webp)
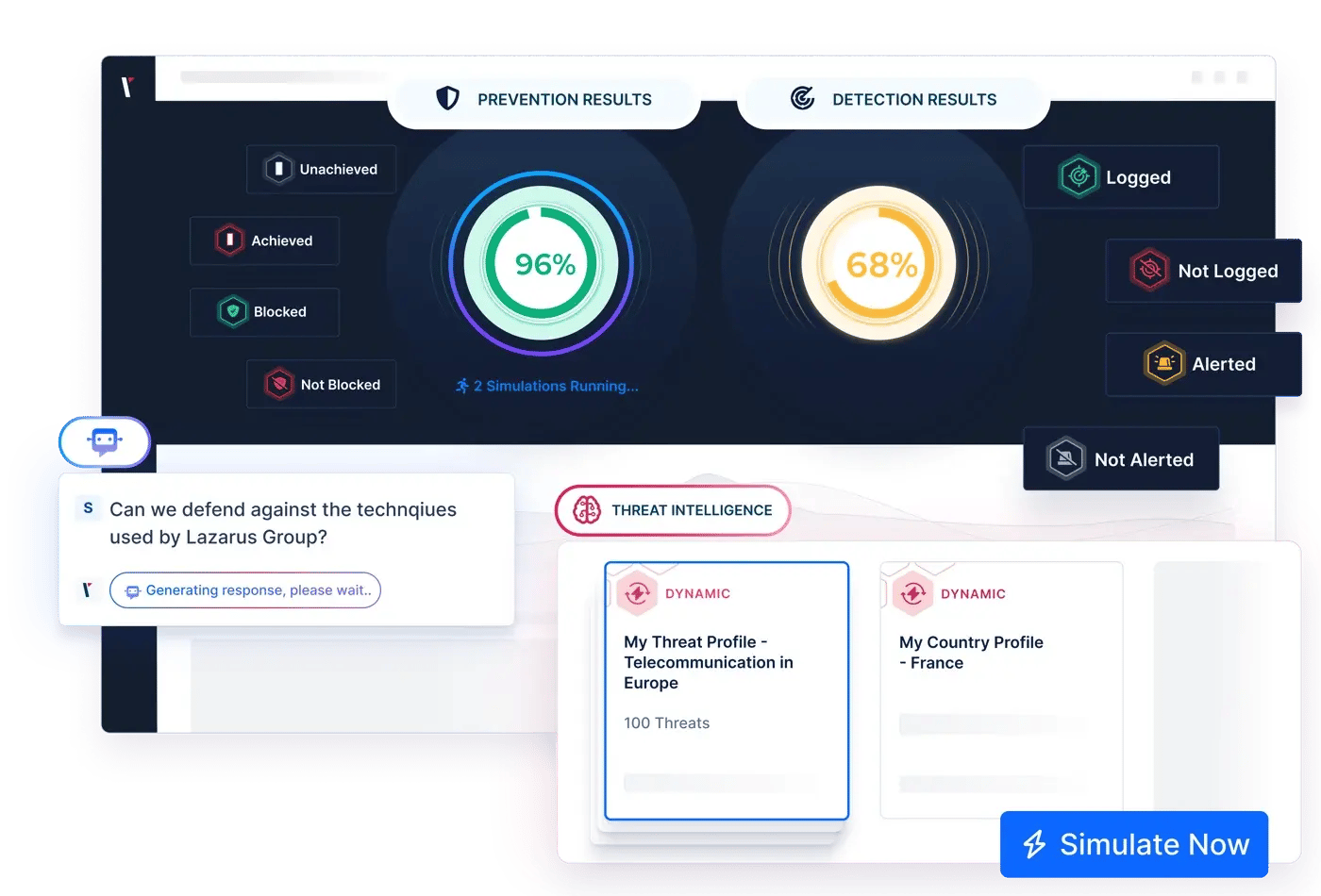

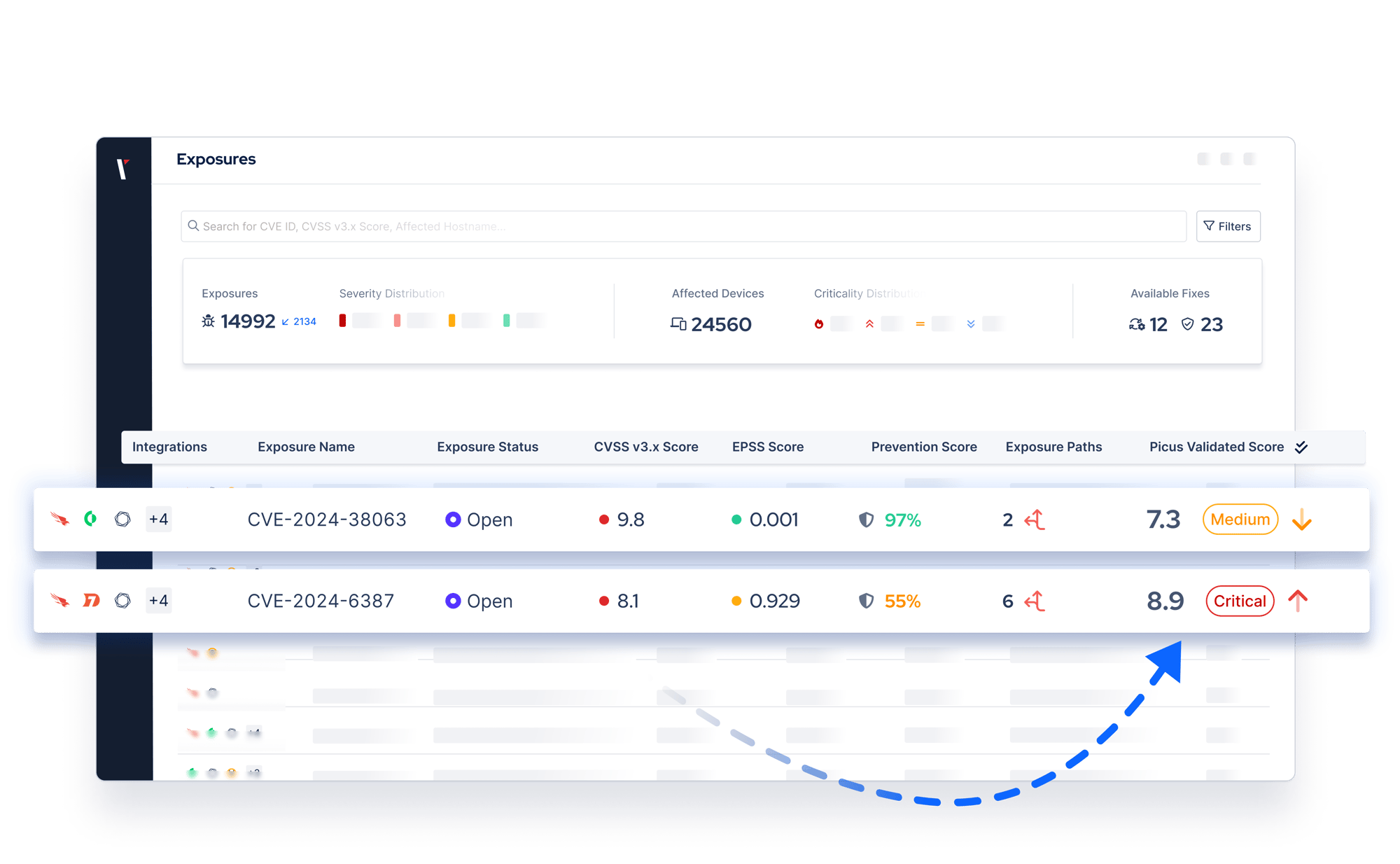
Continuously test your defenses against real-world threats with Picus Security Control Validation (SCV). By verifying which exposures remain exploitable and which controls block them, SCV serves as a foundational pillar of Picus Exposure Validation.
Perform automated pentests to uncover exploitable paths with Picus Attack Path Validation (APV). Picus APV reveals how attackers can progress through your environment, fueling evidence-based prioritization with Picus Exposure Validation.
Unify exposure discovery, control validation, and attack path analysis under a single, continuous validation strategy with Picus Exposure Validation (EXV). Move beyond theoretical severity and align remediation with measurable business impact, operational priorities, and continuous threat exposure management (CTEM) programs.

Setting the Benchmark in Automated Security Validation
Frost & Sullivan recognizes Picus as an Innovation Index Leader and Growth Index Standout in Frost Radar™ 2026.
The analysis highlights Picus’s validation-first strategy, integrations, and exposure validation capabilities aligned with modern CTEM programs.

REQUEST DEMO
Let's Chat!
See what the award-winning Automated Security Validation platform would uncover in your environment.

Frequently Asked Questions
Picus Platform integrates directly with your existing security stack (SIEM, EDR, etc.) with minimal setup, automating the testing and validation process.
Your team saves time and can focus on critical tasks, not on more tools.
If Picus identifies any weaknesses, the platform provides a clear and actionable remediation plan tailored to your specific security setup.
Our platform tells you exactly what failed and how to fix it. Once the fix is applied, you can retest to ensure the issue is resolved, allowing you to move forward with confidence.
The free trial gives you full access to the core functionalities of Picus without a long-term commitment. You’ll be able to test real-world attack simulations, validate your security controls, and see how the platform fits into your current workflow. It’s a risk-free way to experience Picus in action.
Picus platform provides continuous validation and audit-ready reports that align with major compliance standards like PCI-DSS, HIPAA, and ISO 27001. It automatically tracks your security posture, giving you measurable evidence of control effectiveness and helping you stay compliant without the extra workload.

















.png?width=353&height=200&name=Picus-BlueReport2025-Preview2-HubPage%20(2).png)