Identify exposed assets within your environment using Picus Attack Surface Validation (ASV). This visibility feeds into Picus Exposure Validation, uncovering potential entry points and offering critical business context to calculate the Picus Exposure Score.
Vulnerability Prioritization That Reflects Your Reality
Why CVSS Alone Fails at Prioritization
Each year, 40,000+ CVEs emerge, and traditional scores (CVSS, EPSS) label 61% as critical without considering exploitability in your unique environment. Security teams end up flooded by theoretical risks, missing real threats.
When prioritization is based on validation, you know if:
- A “critical” vulnerability is already blocked by your security controls.
- A “medium” vulnerability that opens a path to sensitive data.
You are not short on vulnerability data. You are short on certainty.
Effective Vulnerability Prioritization
High-performing teams prioritize vulnerabilities based on:
Exploitability
Business Impact
Exposure
Control Effectiveness
Attack Path Risk
Compliance Requirements
Expose Which Attacks Can Breach Your Defenses
Picus simulates the entire chain, from initial access to privilege escalation, and delivers detailed findings at every step. You see which controls stop the attack and which gaps remain.

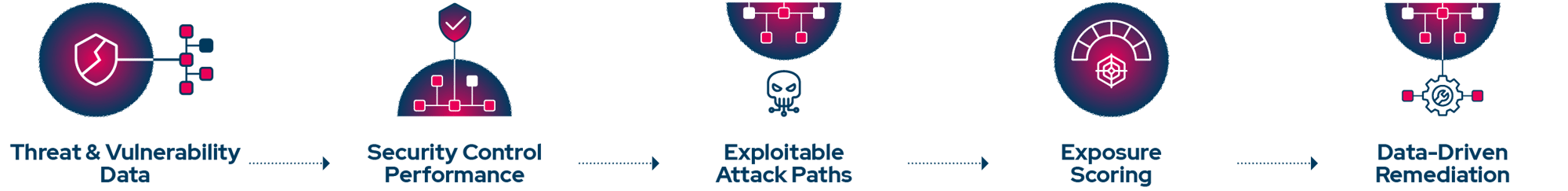
From Vulnerability Data to Exposure-Based Prioritization
By testing vulnerabilities against your specific environment and defenses, Picus ensures that vulnerability prioritization is driven by real business impact, not just CVSS scores.
Capabilities Behind Exposure-Based Prioritization
Only focus on vulnerabilities that can have an actual impact, so your team isn’t overwhelmed trying to remediate everything.




Picus Security Validation Platform
-1.webp?width=1400&height=900&name=Visuals02%20(1)-1.webp)
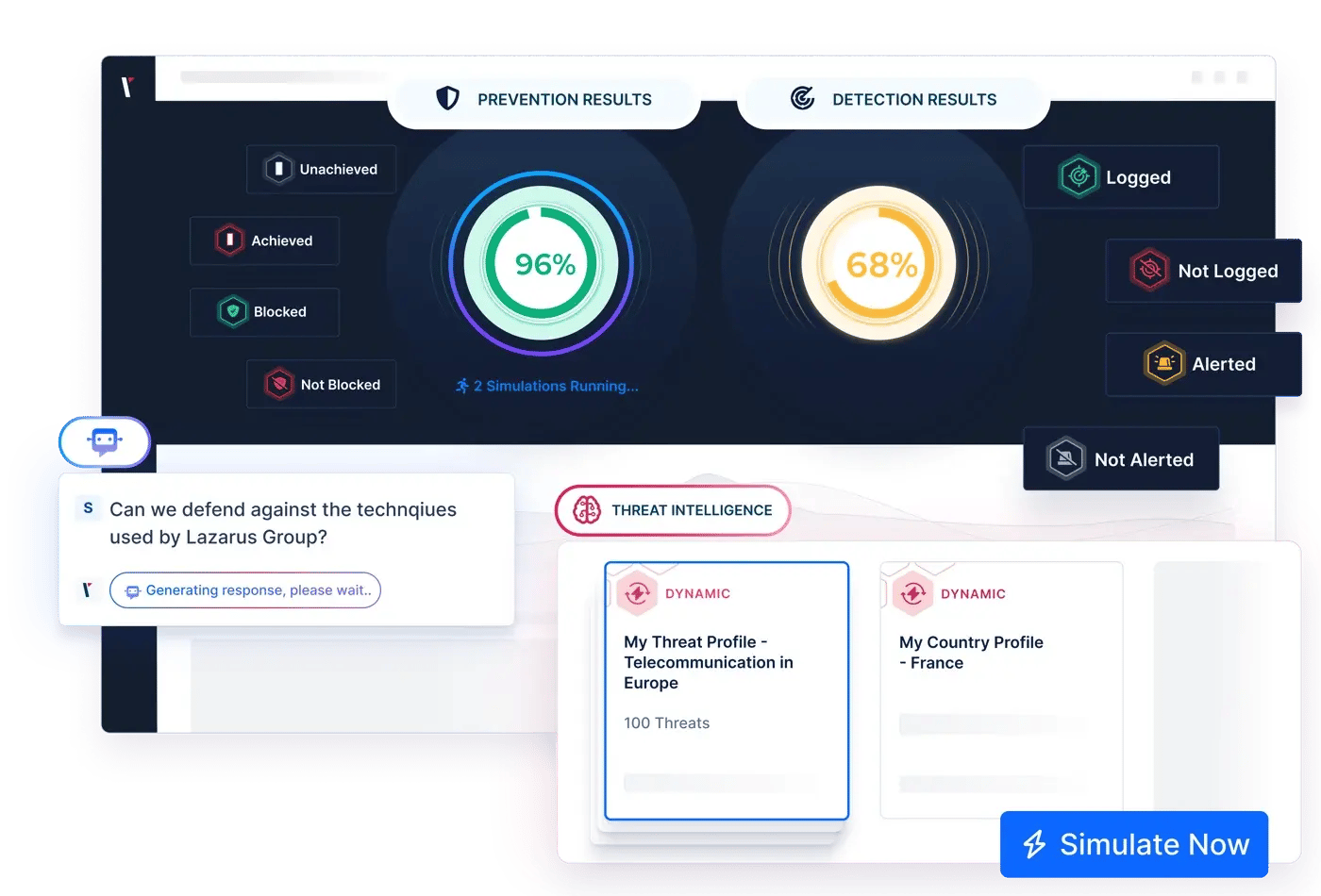

Continuously test your defenses against real-world threats with Picus Security Control Validation (SCV). By verifying which exposures remain exploitable and which controls block them, SCV serves as a foundational pillar of Picus Exposure Validation.
Perform automated pentests to uncover exploitable paths with Picus Attack Path Validation (APV). Picus APV reveals how attackers can progress through your environment, fueling evidence-based prioritization with Picus Exposure Validation.
What You Get from Risk-Driven Prioritization
REQUEST DEMO
Let's Chat!
Discover how your team can reduce noise and remediate vulnerabilities that truly matter.

Frequently Asked Questions
Vulnerability prioritization is the process of ranking identified vulnerabilities based on their risk. Instead of treating all critical or high-severity vulnerabilities as equally important, prioritization evaluates factors such as exploitability, asset importance, business impact, and real-world threat activity.
The purpose of vulnerability prioritization is to help security teams decide what to remediate first when resources are limited. Without prioritization, teams often spend time patching vulnerabilities that are unlikely to be exploited while leaving more dangerous exposures unresolved. Effective prioritization ensures remediation efforts are focused on vulnerabilities that meaningfully reduce organizational risk.
Attack-based vulnerability prioritization evaluates vulnerabilities through the lens of how attackers actually operate. Instead of ranking vulnerabilities in isolation, it considers whether a vulnerability can realistically be used as part of an attack chain to reach valuable assets or cause damage.
This approach incorporates factors such as exploit availability, attacker techniques, lateral movement potential, and privilege escalation paths, and more. A vulnerability may have a lower severity score but still be prioritized if it enables attackers to move deeper into the environment or access sensitive systems.
Attack-based prioritization helps organizations focus on vulnerabilities that contribute to real attack scenarios, rather than theoretical risk.
Vulnerability scanning is about identification. Vulnerability management prioritization is about decision-making.
Scanners generate large volumes of findings by detecting known vulnerabilities across systems, applications, and cloud assets. Prioritization takes those findings and applies context to determine which ones matter most. This includes understanding where the vulnerability exists, how exposed the asset is, whether exploitation is feasible, and what the impact would be if the vulnerability were abused.
In practice, vulnerability management prioritization sits between scanning and remediation. It translates raw scan data into an actionable remediation plan that security, IT, and operations teams can realistically execute.
Effective vulnerability remediation prioritization starts by acknowledging that not all vulnerabilities can or should be fixed immediately. Organizations should prioritize remediation based on a combination of exploitability, security control performance, asset exposure, and business impact.
Rather than aiming for the lowest possible vulnerability count, high-performing teams focus on reducing the likelihood and impact of successful attacks. This means fixing vulnerabilities that attackers are most likely to exploit, and that would cause meaningful damage if compromised. Prioritization should be reviewed continuously as new vulnerabilities, assets, and threats emerge.
Failing to prioritize vulnerabilities properly leads to misallocated effort and increased breach risk. Teams may spend significant time patching vulnerabilities that pose little real danger while leaving exploitable paths open to attackers.
The risk of not patching the right vulnerabilities includes unauthorized access, data breaches, ransomware incidents, operational disruption, and regulatory consequences. Over time, poor prioritization also contributes to remediation fatigue, slower response times, and loss of confidence in vulnerability management programs. Proper prioritization is essential to maintaining both security effectiveness and operational efficiency.






.png?width=416&height=200&name=GSK_Logo%20(1).png)
.png?width=521&height=200&name=packaging-corp-america-logo%20(1).png)
.png?width=511&height=200&name=Pennymac-logo%20(1).png)


.png?width=353&height=200&name=Picus-BlueReport2025-Preview2-HubPage%20(2).png)